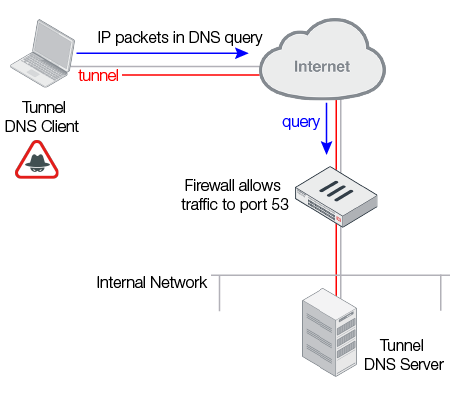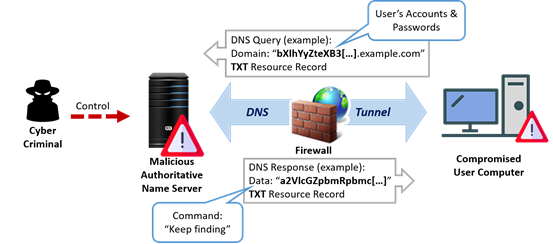
Cyber Attacks Explained - DNS Invasion - Cyber Security Blogs - Valency Networks - Best VAPT Penetration Testing Cyber Security Company - Pune Mumbai Hyderabad Delhi Bangalore Ahmedabad Kolkata India Dubai Bahrain

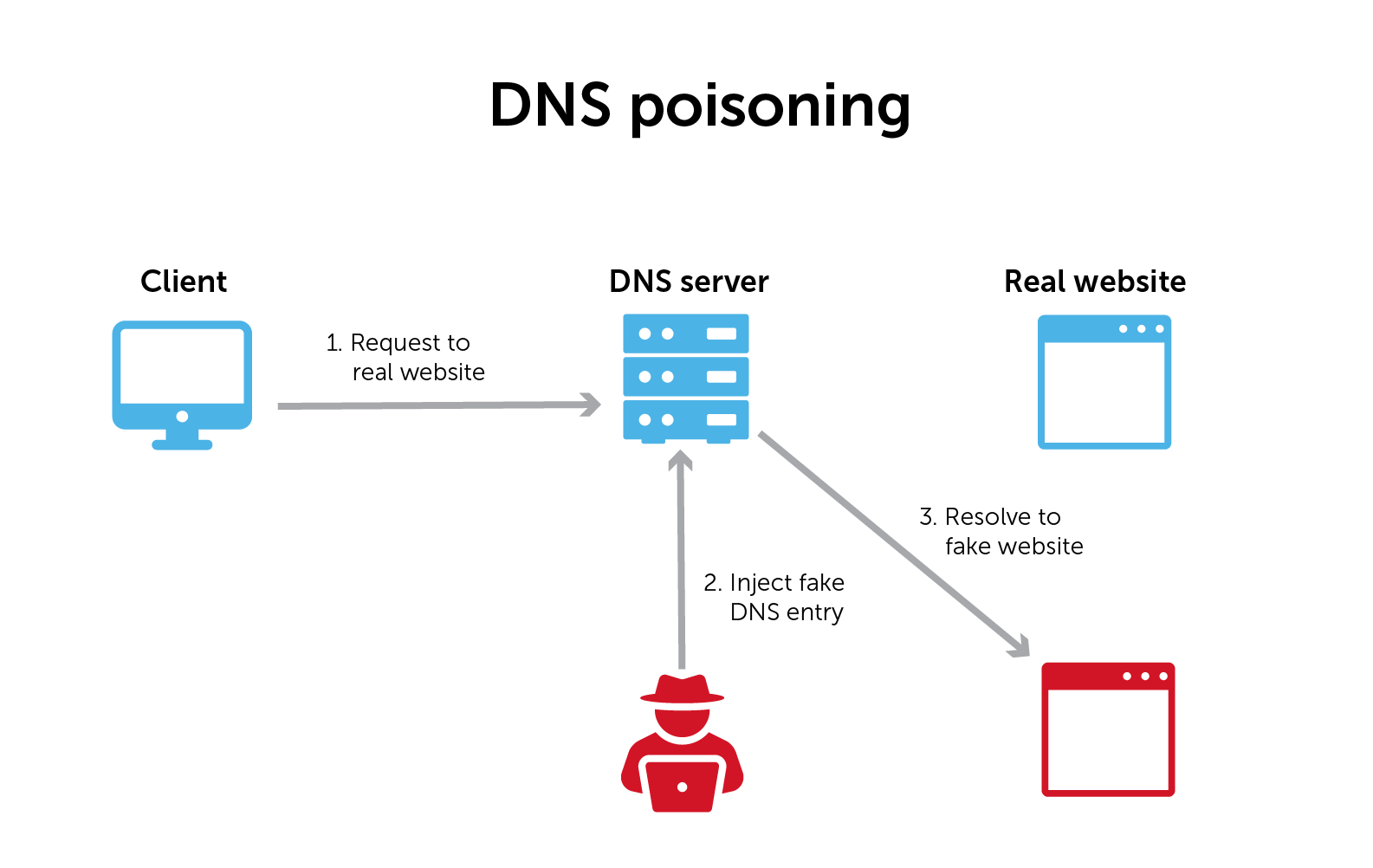
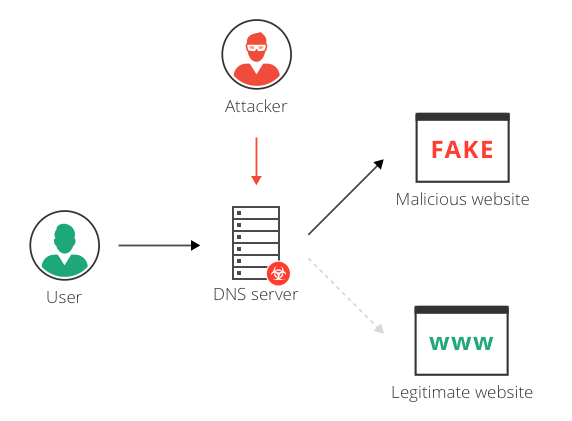
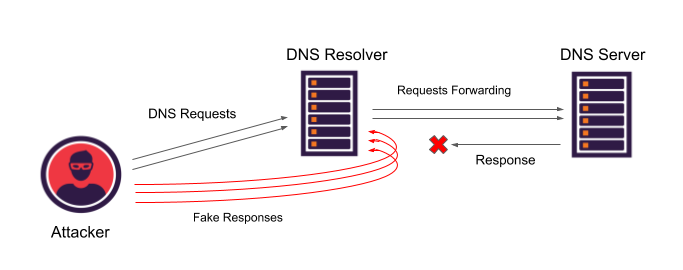
DNS Cache Poisoning. DNS Spoofing the result of alterations… | by Christopher Makarem | IOCSCAN | Medium